Preview release notes
Help us improve our release notes by filling out this short survey.
Current release status
| Current | Upcoming | |
|---|---|---|
| Production | 2023.08.2 | 2023.08.3 Production release is scheduled to begin deployment on September 5 |
| Preview | 2023.08.2 |
2023.08.3 Preview release is scheduled to begin deployment on August 30 |
August 2023
2023.08.0: Monthly Preview release began deployment on August 10
* Features may not be available in all Okta Product SKUs.
Generally Available Features
Okta AD agent, version 3.16.0
When the executor.log and coordinator.log files exceed 5 MB in size, the contents roll over into executor.log.old and coordinator.log.old files.
Okta Active Directory Federation Services Plugin, version 1.7.13
Version 1.7.13 of the Okta Active Directory Federation Services (ADFS) Plugin is now available for download. It includes support for Microsoft Windows Server 2022 and includes bug fixes and security hardening. See Okta ADFS Plugin version history.
Telephony inline hook required for phone authenticator
New orgs now require a Telephony inline hook to use the phone authenticator. You can connect an external telephony provider with Okta using the inline hook. See Phone authenticator. Alternatively, you can acquire the Okta SMS/Voice SKU.
New custom admin role permission
Super admins can now assign View delegated flow permission to their custom admin roles. See About role permissions.
Chrome Device Trust connector integration
With the introduction of the Chrome Device Trust Connector integration for Device Assurance, administrators can create policies that ensure compliance with specific device requirements prior to accessing resources protected by Okta. This integration between Okta and Google facilitates access policies that receive device posture signals directly from a Google API backend, eliminating the need for any agent deployment. As a result, users logging in to a ChromeOS device, or managed Chrome browser, benefit from enhanced authentication security through device security signals.
Authentication challenge for redirects
Users now receive an authentication challenge for each redirect sent to an Identity Provider with Factor only configured, even if the IdP session is active.
Access Testing tool
With the Access Testing tool you can quickly and easily test policies and validate whether your desired security outcomes will be achieved. This tool allows you to simulate user access attributes, such as IP address, device, risk, and so on, to test whether the user will be granted access to the specified application. The tool helps you identify potential security risks and compliance issues before you implement a policy. See Access Testing Tool.
Content security policy enforcement on end-user pages
Content Security Policy is now enforced for end-user pages in orgs with custom domains. Content Security Policy headers help detect attacks such as cross-site scripting and data injection by ensuring browsers know what kind of actions the webpage can execute. Future iterations of the Content Security Policy enforcement for end-user pages will become stricter than this first release. This feature will be gradually made available to all orgs.
Getting Started video for new orgs
The Getting Started page now displays an introductory video. The video provides a quick overview of the common tasks and functions for new orgs, and helps admins familiarize themselves with the Admin Console. See Get started with Okta.
API service integration client secret rotation in the Admin Console
New in this release is the ability to rotate client secrets for an API service integration through the Admin Console. Previously, if a customer wanted to update the client secret for an API service integration, they had to reinstall the integration to obtain a new client ID and secret. There was no option to revoke the client secret while maintaining the client ID and API service integration instance in Okta. With this new feature, customers can generate a new secret, deactivate an old secret, and remove a deactivated secret from the API service integration instance. These functionalities help customers implement security best practices without service downtime. See API Service Integrations.
New event hooks for User Auth Events
Two additional event hooks are now available under User Auth Events:
- User's session was cleared
- User's MFA factor was updated
New application lifecycle event hook
An event hook to deny user access due to a condition in an authentication policy is now available to admins. See Create an event hook .
Polling enhancements for Agentless DSSO
When the server is in SAFE_MODE, Agentless DSSO polling signs in a user if they are in ACTIVE state in Okta.
Early Access Features
Configure management attestation for mobile devices with pre-existing security key
You can now use a pre-existing secret key when you configure Device Management for mobile devices. If you upgrade from Classic Engine, you can reuse your secret key in Identity Engine. See Configure Device Management for mobile devices.
-
OKTA-575884
The Okta Active Directory Federation Services (ADFS) Plugin wrote errors to the plugin log when users attempted to sign in.
-
OKTA-595086
The display of the authorization server Access Policies page froze with large numbers of policies.
-
OKTA-596293
After upgrades to Identity Engine, users were sometimes asked to re-authenticate when refreshing their Okta dashboards even though the sessions were still valid.
-
OKTA-606898
Some users got stuck in a password expiration warning loop when they signed in with AD delegated authentication and updated their password.
-
OKTA-610347
Some orgs couldn't add more than 50 global session policies.
-
OKTA-617816
After orgs upgraded to Identity Engine, the application name in OV Push disappeared.
-
OKTA-626699
On the Administrator assignment by admin page, the Role dropdown list sometimes displayed duplicate admin roles.
-
OKTA-626968
The error message that appeared when the admin attempted to add an inactive Smart Card IdP to the authenticator didn't mention the name of the IdP.
-
OKTA-631657
Users were sometimes improperly redirected to a device-posture provider when none was configured in the authentication policy.
-
OKTA-631752
Adding some IdPs as Factor only caused errors.
-
OKTA-632786
Admins could require Smart Card in an authentication policy even when it wasn't set up as an authenticator.
Applications
New Integrations
New SCIM Integration applications
The following partner-built provisioning integration apps are now Generally Available in the OIN:
-
LeaseHawk: For configuration information, see Okta User Provisioning Integration with SCIM.
SAML for the following Okta Verified applications
-
Apache Kafta: For configuration information, see Configure SAML SSO for Confluent Cloud with Okta Identity Provider.
-
CloudSaver - Tag Manager: For configuration information, see How to Configure SAML 2.0 for CloudSaver Tag Manager for Admins.
-
Current: For configuration information, see Current’s Okta Integration.
-
Jasper AI: For configuration information, see Configuring Jasper Single Sign-On (SSO).
-
Kolide: For configuration information, see How to configure SAML for Kolide.
-
Reasons for Access: For configuration information, see Configuring Reasons for Access with Okta.
-
Teamspective: For configuration information, see Okta SAML Single Sign-On (SSO) for Teamspective.
OIDC for the following Okta Verified applications
-
AlphaSOC Console: For configuration information, see Okta SSO Integration.
-
Everlaw: For configuration information, see Organization Admin: Single Sign-On.
-
Flike: For configuration information, see Okta SSO Configuration Guide.
-
LeaseHawk: For configuration information, see How to Configure OIDC for LeaseHawk with Okta.
-
Valos: For configuration information, see Logging in with Okta Single Sign-On (SSO).
-
Yooz: For configuration information, see How to configure OIDC for Yooz.
-
Zello: For configuration information, see Okta SSO Configuration Guidelines.
Weekly Updates
Fixes
-
OKTA-619028
Read-only admins received user reports of suspicious activity email notifications in error.
-
OKTA-624193
The Access Testing Tool results showed an incorrect value for the profile enrollment self-service registration option.
-
OKTA-627533
Removing the emailAuthenticationLink variable from the email template didn't update the Sign-In Widget.
-
OKTA-631142
Orgs using a custom client_id in their OAuth2 client apps were unable to delete enrolled users.
-
OKTA-632131
OpenID Connect /token requests using the SAML 2.0 Assertion grant type flow failed if the SAML assertion expiry was greater than 30 days.
-
OKTA-632850
Slack provisioning didn't automatically retry after exceeding rate limits.
-
OKTA-633585
The on-demand auto-update banners for the Active Directory agent displayed updates in a random order.
-
OKTA-634923
Users weren't present in the import queue after being unassigned from an app.
-
OKTA-635579
When a super admin went to the tab, the Edit group assignments button was mislabeled.
-
OKTA-636652
The Administrators page wasn’t translated to Japanese.
Applications
Application Update
-
Group push and group import is now available for the Smartsheet SCIM integration.
New Integrations
New SCIM Integration applications
The following partner-built provisioning integration apps are now Generally Available in the OIN Catalog as partner-built:
-
Skippr for Organizations: For configuration information, see Skippr for Organizations with SCIM 2.0.
SAML for the following Okta Verified applications:
-
9Line: For configuration information, see Okta SAML SSO Configuration.
-
Blameless: For configuration information, see How to Configure SAML 2.0 for Blameless for admins.
-
Fathom: For configuration information, see SAML 2.0 Configuration Guide.
-
Y42: For configuration information, see Okta.
OIDC for the following Okta Verified applications:
-
rule5: For configuration information, see rule5 Okta Configuration Guide.
-
QuotaPath: For configuration information, see Okta SSO.
-
Rupert: For configuration information, see Rupert Okta SSO Configuration.
Fixes
-
OKTA-621214
Long custom label text was sometimes truncated on the Sign-In Widget during enrollment.
-
OKTA-621253
Email Change Confirmed Notification messages weren't sent if the audience was set to Admin only.
-
OKTA-627175
Some tasks displayed a greater-than sign (>) instead of the date.
-
OKTA-630368
RADIUS logs showed multiple, repetitious Invalid cookie header warning messages.
-
OKTA-634010
Users who were locked out of Okta but not Active Directory could receive Okta Verify push prompts and sign in to Okta.
-
OKTA-637641
Some users received a Bad Request error when they signed in with Okta FastPass.
-
OKTA-639427
When admins added a new user in Preview orgs, the Realm attribute appeared on the dialog.
Applications
New API Service Integration applications:
-
Sysdig: For configuration information, see Okta Integration.
OIDC for the following Okta Verified applications:
-
AskFora: For configuration information, see AskFora Okta Configuration Guide.
FastPass phishing resistance for unmanaged iOS devices
While Okta FastPass can protect users against most phishing attacks, it can’t secure authentication on unmanaged iOS devices. To close this gap, Okta is rolling out phishing resistance for Okta FastPass on unmanaged iOS devices. With this change, users who authenticate with Okta FastPass on their personal or unmanaged iOS devices are protected from phishing attacks. See About MFA authenticators.
Okta ThreatInsight coverage on core Okta API endpoints
Okta ThreatInsight coverage is now available for core Okta API endpoints (OpenID Connect & OAuth 2.0, Okta Management, and MyAccount API). Based on heuristics and machine learning models, Okta ThreatInsight maintains an evolving list of IP addresses that consistently show malicious activity across Okta's customer base. Requests from these bad IP addresses can be blocked or elevated for further analysis when Okta ThreatInsight is enabled for an Okta org.
Previously, Okta ThreatInsight coverage only applied to Okta authentication endpoints (including enrollment and recovery endpoints). With this release, enhanced attack patterns are detected for authentication endpoints and limited attack patterns are also detected for non-authentication endpoints.
There are no changes to the existing Okta ThreatInsight configuration. You can still enable Okta ThreatInsight with log and block mode, log mode, and exempt network zones. A new Negative IP Reputation reason is available for high security.threat.detected events. See System Log events for Okta ThreatInsight.
Application Entitlement Policy
Administrators can now override attribute mapping when assigning apps to individuals or groups. Attributes can also be reverted to their default mappings. See Override application attribute mapping. This feature will be gradually made available to all orgs.
Assign admin roles to an app
Orgs can now assign admin roles to their custom API Service Integrations. Apps with assigned admin roles are constrained to the permissions and resources that are included in the role assignment. This helps ensure that apps only have access to the resources that are needed to perform their tasks, and improves orgs' overall security. See Work with the admin component.
Descriptive System Log events
When Okta identifies a security threat, the resulting security.threat.detected entry now provides a descriptive reason for the event. See System Log.
Improvements to the self-service registration experience
Earlier versions of the self-service registration (SSR) flow used a complicated array of templates to send activation emails to end users. The simplified SSR flow reduces this to only two email templates with customized welcome messages. If your application requires immediate verification of the end user’s email address, Okta uses the Registration - Activation template. This template includes a magic link for a smoother sign-in experience. If email verification isn't immediately required to sign in to the application, Okta uses the Registration - Email Verification template. This template includes a link for end users to complete email verification at any time after they successfully sign in to the application. See Customize email notifications and the Okta email (magic link/OTP) integration guide.
New App Drawer
The updated app settings panel on the Okta End-User Dashboard allows end users to see all app details in a single view without having to expand multiple sections. End users can quickly differentiate between SWA apps where they have set a username and password and SAML / OIDC apps that are admin-managed with no additional user settings. The updated app settings panel also provides accessibility improvements with better screen reader support and color contrast. See View the app settings page.
SSO apps dashboard widget
The new SSO apps widget displays the number of user sign-in events across each of your org’s apps over a selected period of time. You can use it to see which apps are used most frequently and to easily monitor the authentication activity across your org. See Monitor your apps.
Improvements to the self-service unlock process
Earlier versions of the self-service unlock (SSU) flow created unnecessary friction in the end user experience. The newly enhanced SSU feature introduces a seamless magic link experience in emails sent out to unlock accounts. Users no longer need to provide consent when using the same browser. In addition, after successfully unlocking their account, clicking the email magic link counts towards the application's assurance policy. After the assurance requirements are met, the user is signed directly in to the application. See Configure the Email authenticator.
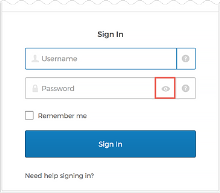
Toggle password visibility on the Okta Sign-In page
End users can now toggle visibility of their password on the Sign-In Widget, allowing them to check their password before they click Sign In. Note that passwords are visible for 30 seconds and then hidden automatically. See Authentication. See Enable delegated authentication.
Email failure events in the System Log
Admins can now view email delivery failure events in the System Log. This helps admins better monitor the email event activity in their org. See System Log.
Shareable Authentication Policies
Admins can now manage authentication policies using a centralized view. While authentication policies allowed admins the ability to make application access decisions using user, device, and other contextual information, managing these policies across hundreds of applications became challenging and error-prone. On the new Authentication Policies page, admins can create new policies, apply those policies to multiple applications, and assess what application access decisions are impacted by each policy. Two policy name changes are included in this release: app sign-on policy is renamed authentication policy, and Okta sign-on policy is renamed Global Session Policy. See Authentication policies.
Choose additional filters for Office 365 sign-on policy
Filters have been added to enable admins to distinguish between web browsers and Modern Authentication clients when creating an app sign-on policy. See Office 365 sign-on rules options.
Device Authorization grant type
Advancements in internet technology have seen an explosion of smart devices and the Internet of Things. Consumers need to sign in to applications that run on these devices, but the devices either lack support for a web browser or have limited ability for input, such as smart TVs, car consoles, and thermostats. As a result, users resort to insecure authentication solutions that are error-prone and time-consuming.
The Device Authorization grant feature is an OAuth 2.0 grant type that allows users to sign in to input-constrained devices and also to devices that lack web browsers. This feature enables users to use a secondary device, such as a laptop or mobile phone, to complete sign-in to applications that run on such devices. See Configure Device Authorization.
User Verification options for admins
In the Admin Console, admins can now configure whether end users are required to provide biometrics for device enrollment. See Enable Okta FastPass
Manage admin email notification subscriptions using API endpoints
Admins can manage email subscriptions using the Admin Email Subscription API endpoints.
-
Super admins can configure default subscription settings by admin type.
-
All admins can manage their own admin email notification subscriptions.
End-User Dashboard and Plugin redesign
The Okta End-User Dashboard and Okta Browser Plugin have been redesigned with a modern look and feel that includes new sidebar navigation, fuzzy search, and sections that replaces tabs.
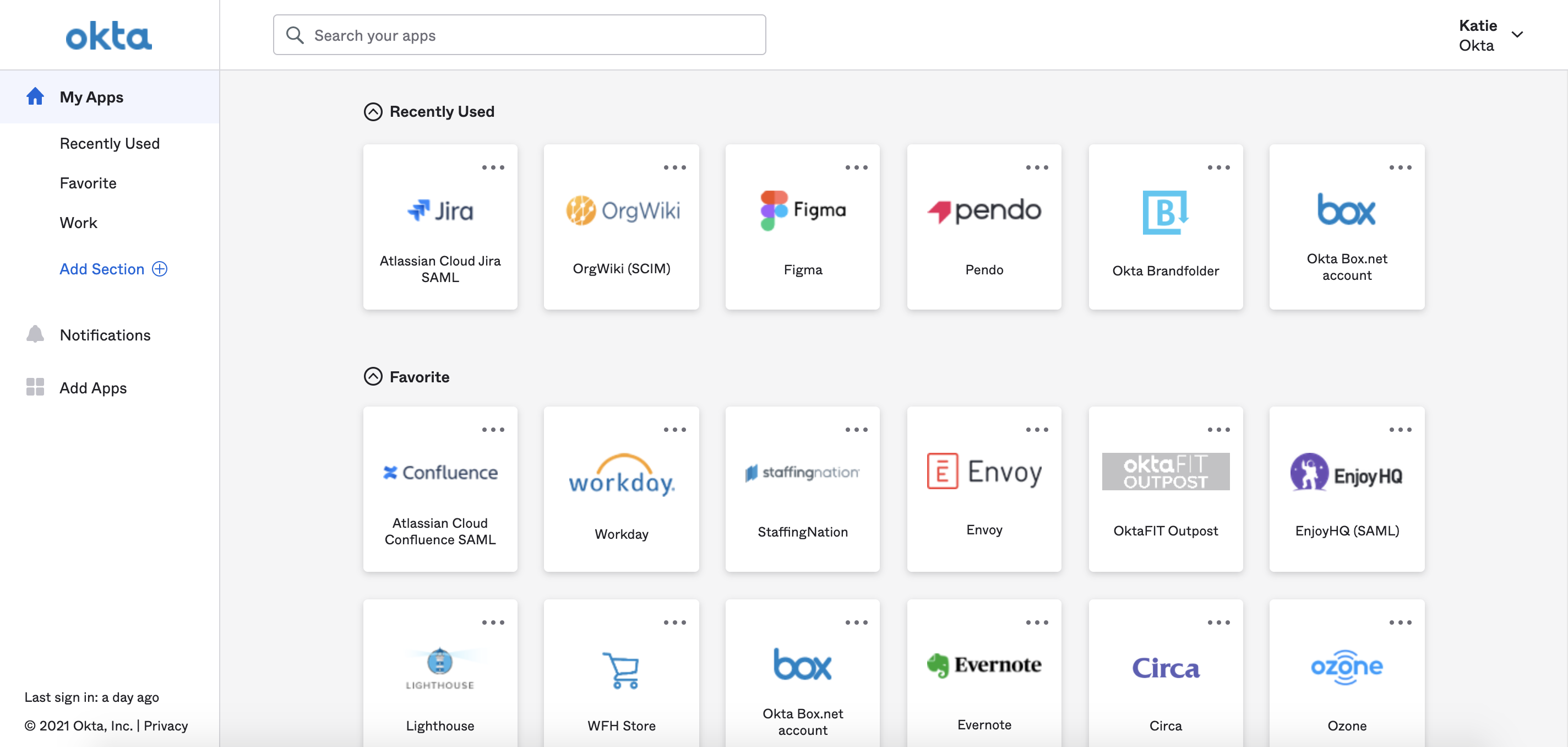
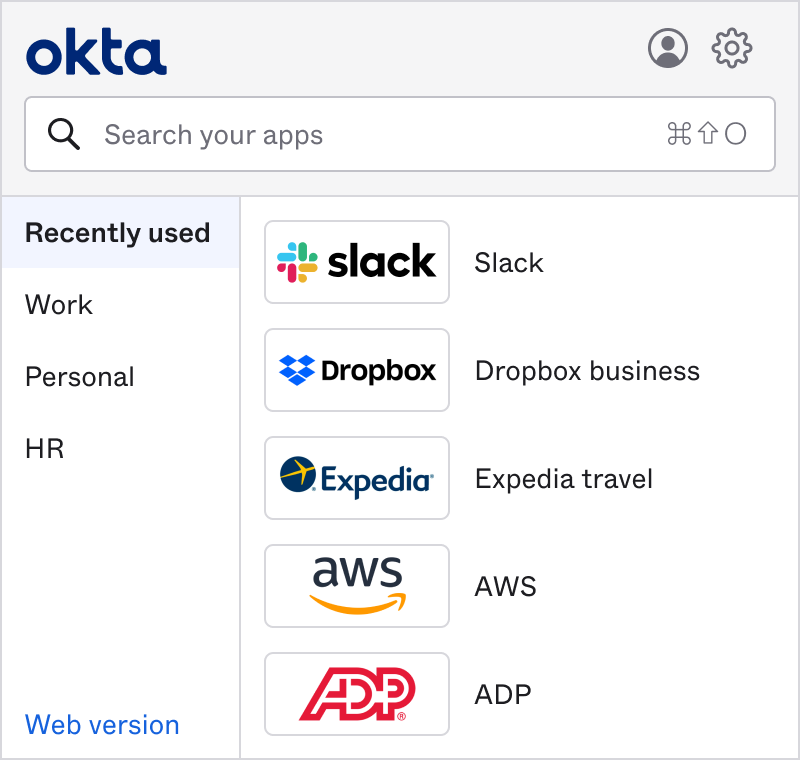
Admins can enable this new design all at once or by groups. The new experience is 50% faster, more intuitive to use, and more responsive to smaller screens. Design changes also improve accessibility and app discovery for end users.
See Create sign-on policies with Okta Applications.
This feature will gradually be made available to all Preview orgs.
Workflows Templates available
Workflows Templates is now available, providing users with access to a searchable catalog of installable Flows that address many common use cases. See Get started with Workflows Templates.
LDAP password reset option
LDAP delegated authentication settings can now be configured to allow users to reset their passwords. This change reduces the time needed for password management and allows users to reset their passwords quickly and easily. See Enable delegated authentication.
LDAP admin password reset
For orgs integrated with LDAP, admins can now perform password resets for an active individual end user. See Reset a user password.
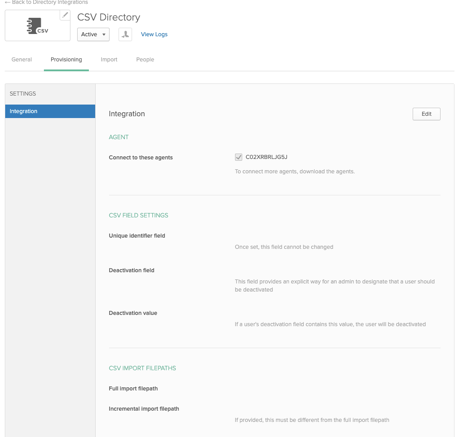
Incremental Imports for CSV
Incremental imports improve performance by importing only users who were created, updated, or deleted since your last import. See Manage your CSV directory integration. Note that this feature is being re-released having previously been released to Production in 2020.09.0.
Password changed notification email
To eliminate unnecessary email notifications, the Password changed notification email setting is no longer enabled by default on new preview orgs. See Password changed notification for end users.
Office 365 Silent Activation
Using Okta as the Identity Provider, Okta Office 365 Silent Activation allows for a seamless experience for your Microsoft Office 365 end users accessing Office 365 apps on domain joined shared Workstations or VDI environments. Once your end users have logged into a domain-joined Windows machine, no further activation steps are required. See Office 365 Silent Activation: New Implementations.
End-user Welcome emails localized
The ability to localize the Welcome email that Okta sends to new end users by referencing the users' default locale property is now Generally Available. See Configure general customization settings.
People page improvements
The People page has been improved so the people list can be filtered by user type. See Universal Directory custom user types known issues.
Mobile tab available for mobile-capable apps
The Mobile tab available in the Okta Admin Console for mobile-capable OIN apps allows you to publish mobile applications to an App Store and deploy them to your end users.
See Enable access to managed mobile apps
Provisioning page UI element change
Drop-down menus on the Provisioning page (General Settings) were standardized.
UI element change
Drop-down menus on the Provisioning page (General Settings) are standardized. See Provision applications.
Early Access features, auto-enroll
You can now opt to auto-enroll in all Early Access features, instead of having to enable them as they become available. For more information, see Manage Early Access features.
Connecting Apps to Okta using the LDAP Interface
The LDAP Interface allows you to authenticate legacy LDAP apps to Universal Directory in the cloud. With the LDAP Interface, authentication is done directly against Okta via LDAP, without the need for an on-premise LDAP server. In addition, the LDAP interface supports other LDAP functions like search. See Set up and manage the LDAP Interface.